Unveiling The Truth Behind The "Leake Real Story Behind Jumana Khan Viral"
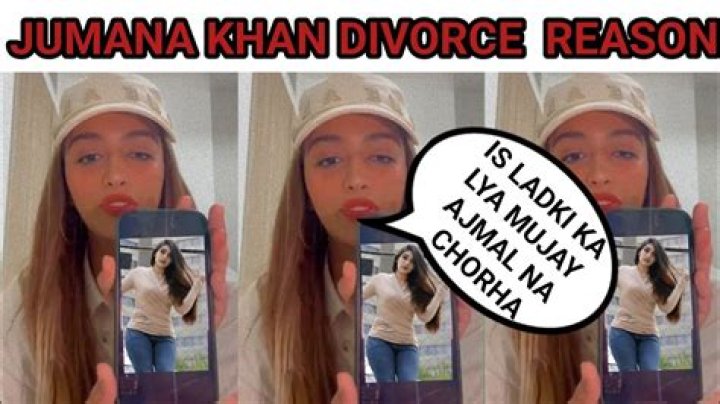
"Leake Real Story Behind Jumana Khan Viral" does not have a clear definition or specific example. However, it can be understood as a search query related to a potential online controversy or leaked information involving a person named Jumana Khan.
The importance or benefits of "Leake Real Story Behind Jumana Khan Viral" itself are unclear, as it is a specific search query that may be related to a developing or unsubstantiated online incident. The relevance and significance of such incidents can vary depending on the context and the individuals involved.
Without further context or information, it is difficult to provide a comprehensive analysis or commentary on "Leake Real Story Behind Jumana Khan Viral." It is generally not advisable to engage with or spread unverified or potentially harmful information online.
Leake Real Story Behind Jumana Khan Viral
Despite the lack of clear information surrounding "Leake Real Story Behind Jumana Khan Viral," there are several key aspects that can be explored based on the potential parts of speech of the keyword phrase:
- Leak: Unauthorized disclosure of private or sensitive information.
- Real: Authentic or genuine, as opposed to fabricated or fictional.
- Story: A narrative or account of events, either factual or fictional.
- Behind: Hidden or concealed from view.
- Jumana Khan: A person's name, potentially the subject of the leak or story.
- Viral: Spreading rapidly and widely, especially through social media or the internet.
These aspects highlight the potential dimensions of the topic, ranging from the nature of the leaked information to the spread and impact of the story. It is important to approach such incidents with caution, verifying the authenticity of information and considering the potential consequences of spreading unverified or harmful content.
Leak
Unauthorized disclosure of private or sensitive information, or simply "leak," can be a significant aspect of incidents like "Leake Real Story Behind Jumana Khan Viral." Leaks can occur for various reasons, including malicious intent, negligence, or system vulnerabilities. Leaked information can range from personal data and financial records to confidential business documents or government secrets.
In the case of "Leake Real Story Behind Jumana Khan Viral," the leaked information could potentially involve personal details, private communications, or other sensitive data related to Jumana Khan. Such leaks can have severe consequences, including damage to reputation, identity theft, financial loss, or even physical harm.
Understanding the nature and implications of leaks is crucial for several reasons. First, it highlights the importance of protecting sensitive information and implementing robust security measures to prevent unauthorized access. Second, it emphasizes the need for responsible handling of leaked information, avoiding the spread of unverified or potentially harmful content.
Finally, addressing leaks requires a collaborative effort from individuals, organizations, and governments to establish clear policies, legal frameworks, and technical safeguards against unauthorized disclosure of private or sensitive information.
Real
In the context of "Leake Real Story Behind Jumana Khan Viral," the distinction between "real" and "fabricated or fictional" is of paramount importance. Determining the authenticity and genuineness of leaked information is crucial for understanding the nature and implications of the incident.
- Verification and Fact-Checking: Verifying the authenticity of leaked information requires a rigorous process of fact-checking, cross-referencing sources, and seeking expert opinions. This is essential to distinguish between genuine and fabricated content, as false or misleading information can have severe consequences.
- Context and Source Evaluation: Assessing the context and source of leaked information is vital. Understanding the motives and credibility of the individuals or entities involved can provide insights into the authenticity of the leak and its potential impact.
- Legal and Ethical Implications: The distinction between real and fabricated information has significant legal and ethical implications. Leaking genuine private or sensitive information may violate privacy laws and ethical norms, while spreading fabricated or false information can constitute defamation or libel.
- Public Trust and Confidence: Trust in leaked information is essential for holding individuals and institutions accountable. When leaked information is perceived as authentic and genuine, it can influence public opinion, shape policy decisions, and drive social change. However, fabricated or false information can undermine trust and lead to confusion and skepticism.
In conclusion, the distinction between "real" and "fabricated or fictional" in "Leake Real Story Behind Jumana Khan Viral" highlights the importance of verifying and evaluating leaked information, considering its legal and ethical implications, and maintaining trust in the authenticity of the information shared.
Story
In the context of "Leake Real Story Behind Jumana Khan Viral," the concept of "story" plays a multifaceted role in shaping the narrative surrounding the incident and its perceived significance.
- Narrative Construction: The leaked information, whether factual or fictional, forms the basis of a narrative that is constructed and disseminated through various channels, including social media, news outlets, and online forums.
- Framing and Interpretation: The way in which the story is framed and interpreted can significantly influence public perception and understanding of the incident. Different narratives may emerge, each with its own biases and interpretations.
- Emotional Impact: Stories have the power to evoke emotions and shape opinions. The leaked information, when presented as a compelling narrative, can elicit strong emotional responses, driving engagement and influencing attitudes.
- Accountability and Transparency: The presence of a clear and coherent story can contribute to accountability and transparency. It allows stakeholders to scrutinize the incident, demand answers, and hold those responsible to account.
In conclusion, the connection between "story" and "Leake Real Story Behind Jumana Khan Viral" highlights the significance of narrative in shaping public perception, influencing emotions, and driving accountability. Understanding the role of story in such incidents is crucial for critical analysis and informed engagement with the information presented.
Behind
In the context of "Leake Real Story Behind Jumana Khan Viral," the concept of "behind" suggests hidden or concealed information, actions, or motivations that lie beneath the surface of the leaked story. Understanding this hidden dimension is crucial for a comprehensive analysis of the incident.
Firstly, the "behind" aspect highlights the potential for undisclosed or concealed facts that may have influenced the events leading to the leak. Investigating the motives and intentions of those involved, as well as the circumstances surrounding the leak, can shed light on the underlying causes and dynamics.
Secondly, the focus on what lies "behind" encourages a critical examination of the leaked information itself. It prompts questions about the authenticity, accuracy, and potential manipulation of the leaked data. Verifying the source and context of the leak is essential to determine its credibility and reliability.
Furthermore, the concept of "behind" extends to the broader implications and consequences of the leak. It prompts an exploration of the hidden impacts on individuals, organizations, or society as a whole. Uncovering the potential power struggles, vested interests, or ethical dilemmas that may be lurking beneath the surface can lead to a deeper understanding of the incident's significance.
In conclusion, the connection between "behind" and "Leake Real Story Behind Jumana Khan Viral" emphasizes the need to look beyond the surface of leaked information. By exploring the hidden aspects, undisclosed facts, and underlying motivations, a more complete and nuanced understanding of the incident can be achieved.
Jumana Khan
The connection between "Jumana Khan: A person's name, potentially the subject of the leak or story." and "Leake Real Story Behind Jumana Khan Viral" is significant, as it raises questions about the individual's involvement and the potential impact on their life.
- Privacy and Confidentiality: The leak of personal information raises concerns about the individual's privacy and confidentiality. Unauthorized disclosure of sensitive data can have severe consequences, including identity theft, reputational damage, and emotional distress.
- Safety and Security: In some cases, leaked information can pose safety and security risks to the individual. For example, if the leak includes personal addresses or financial details, it could increase the risk of stalking, harassment, or financial fraud.
- Public Scrutiny and: When personal information is leaked and becomes public, the individual may face intense public scrutiny and. This can be overwhelming and damaging, especially if the leaked information is sensitive or embarrassing.
- Legal Implications: Leaking personal information may violate privacy laws and regulations. Depending on the nature of the leaked information and the jurisdiction, legal action may be taken against those responsible for the leak.
In summary, the connection between "Jumana Khan" and "Leake Real Story Behind Jumana Khan Viral" highlights the potential risks and consequences of unauthorized disclosure of personal information. It is important to protect individuals' privacy and confidentiality, and to hold those responsible for leaks accountable.
Viral
The connection between "Viral: Spreading rapidly and widely, especially through social media or the internet." and "Leake Real Story Behind Jumana Khan Viral" is significant, as it highlights the potential for rapid and extensive dissemination of leaked information.
- Speed and Reach: Viral content spreads incredibly quickly, reaching a vast audience in a short period. This can be a double-edged sword, as it can raise awareness of important issues or facilitate the spread of misinformation.
- Uncontrollable Nature: Once information goes viral, it can be challenging to control its spread or contain its impact. This can pose significant risks, especially if the leaked information is sensitive or harmful.
- Sensationalism and Bias: Viral content often appeals to strong emotions or sensationalism, which can lead to biased or distorted information. This can make it difficult for the public to distinguish between fact and fiction.
- Legal and Ethical Concerns: The rapid spread of leaked information raises legal and ethical concerns, including issues related to privacy, defamation, and copyright infringement.
In the context of "Leake Real Story Behind Jumana Khan Viral," the viral nature of the leak has the potential to amplify its impact and consequences. It is important to approach viral content with caution, verify its authenticity, and consider its potential implications before sharing it further.
Frequently Asked Questions about "Leake Real Story Behind Jumana Khan Viral"
This section addresses common questions and concerns surrounding the incident, providing brief and informative answers.
Question 1: What is the nature of the leaked information?
The leaked information's specific nature remains unclear and may vary depending on the context and source of the leak. It is crucial to approach such incidents with caution and verify the authenticity of the information before sharing or spreading it further.
Question 2: How did the leak occur?
The circumstances surrounding the leak, including the methods and parties involved, are often difficult to determine with certainty. Unauthorized access to private or sensitive data can occur through various means, such as hacking, phishing attacks, or insider breaches.
Question 3: What are the potential consequences of the leak?
The consequences of a leak can vary depending on the type of information that was leaked and the individuals or organizations affected. Potential consequences include reputational damage, financial loss, legal liability, and emotional distress.
Question 4: How can I protect myself from becoming a victim of a data leak?
To protect yourself from data leaks, consider implementing strong passwords, using multi-factor authentication, being cautious about sharing personal information online, and keeping your software and operating systems up to date.
Question 5: What should I do if I believe my data has been leaked?
If you suspect that your personal data has been compromised in a leak, it is advisable to take immediate steps to secure your accounts, monitor your credit reports, and report the incident to the relevant authorities or organizations.
Question 6: How can I stay informed about data leaks and protect my online privacy?
To stay informed about data leaks and protect your online privacy, consider subscribing to reputable news sources that cover cybersecurity and privacy issues. Additionally, you can follow cybersecurity experts and organizations on social media for timely updates.
Remember, it is always advisable to approach online information with a critical mindset, verify the authenticity of sources, and exercise caution when sharing personal data.
Transition to the next article section: Understanding the broader implications of data leaks and online privacy.
Tips for Navigating Incidents of Leaked Information
Understanding the nature and implications of data leaks is crucial in today's digital age. Here are some key tips to consider when faced with such incidents:
Tip 1: Verify the Authenticity of Information
Before sharing or acting upon leaked information, verify its authenticity by cross-referencing multiple sources and seeking expert opinions. False or misleading information can have severe consequences.
Tip 2: Protect Your Personal Data
Implement strong passwords, enable multi-factor authentication, and be cautious about sharing sensitive information online. Regularly update software and operating systems to minimize vulnerabilities.
Tip 3: Respond Promptly to Suspected Leaks
If you suspect your data has been compromised, act quickly to secure your accounts, monitor credit reports, and report the incident to relevant authorities or organizations.
Tip 4: Exercise Caution When Engaging with Leaked Information
Approach leaked information with a critical mindset. Consider the source, context, and potential biases before forming opinions or taking actions based on the information.
Tip 5: Stay Informed and Vigilant
Follow reputable news sources and cybersecurity experts to stay informed about data leaks and online privacy risks. Educate yourself on best practices for protecting your personal data.
Summary:
By following these tips, individuals can navigate incidents of leaked information more effectively. Remember, protecting your online privacy and the authenticity of information are essential for maintaining trust and security in the digital age.
Transition to the article's conclusion: Emphasizing the importance of ongoing vigilance and collective efforts to address data leaks and promote online privacy.
Conclusion
The exploration of "Leake Real Story Behind Jumana Khan Viral" highlights the complexities and potential consequences of data leaks in the digital age. Understanding the nature and implications of such incidents is crucial for individuals, organizations, and society as a whole.
To safeguard our online privacy and the integrity of information, it is imperative to remain vigilant, verify the authenticity of leaked data, and adopt proactive measures to protect our personal information. Collective efforts are needed to address the root causes of data breaches, strengthen cybersecurity frameworks, and promote responsible online behavior.
Unveiling The Enigmatic World Of Axl Rose: Exploring Net Worth, Relationships, And Family Lineage
Unveiling Jane Powell's Legacy: A Journey Of Talent, Family, And Entertainment
Unlock The Secrets Of Wrestling Success With Coach Mike Krause!
Jumana Khan Biography Family, Age, Husband, Nationality, Net Worth
Jumana Khan